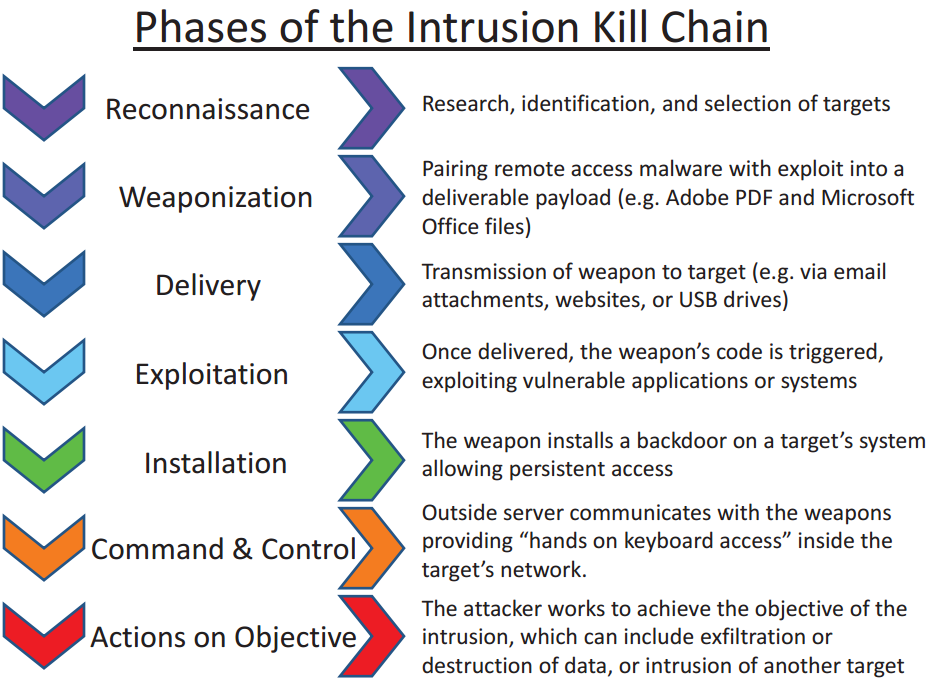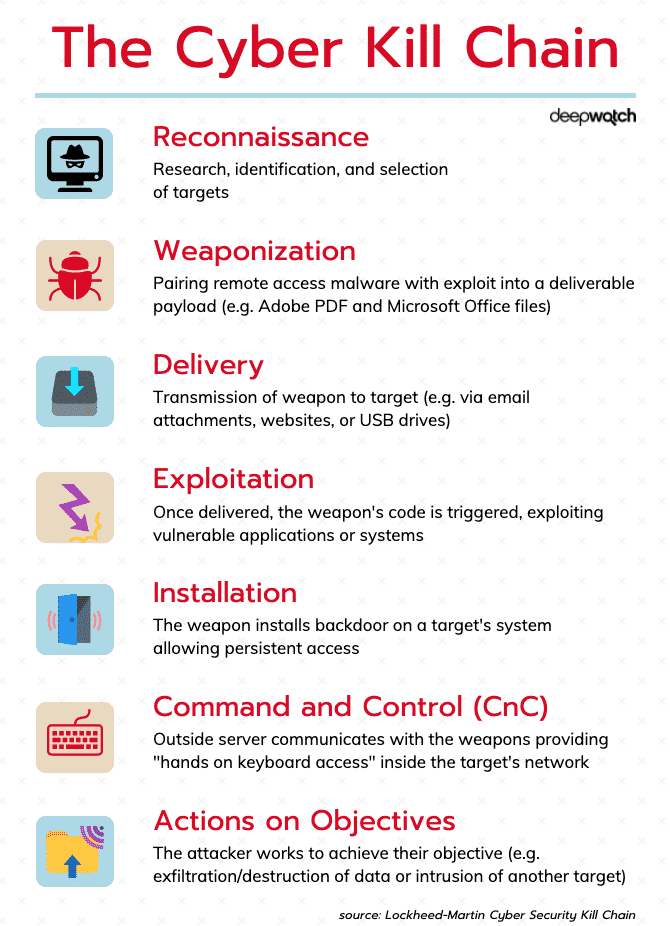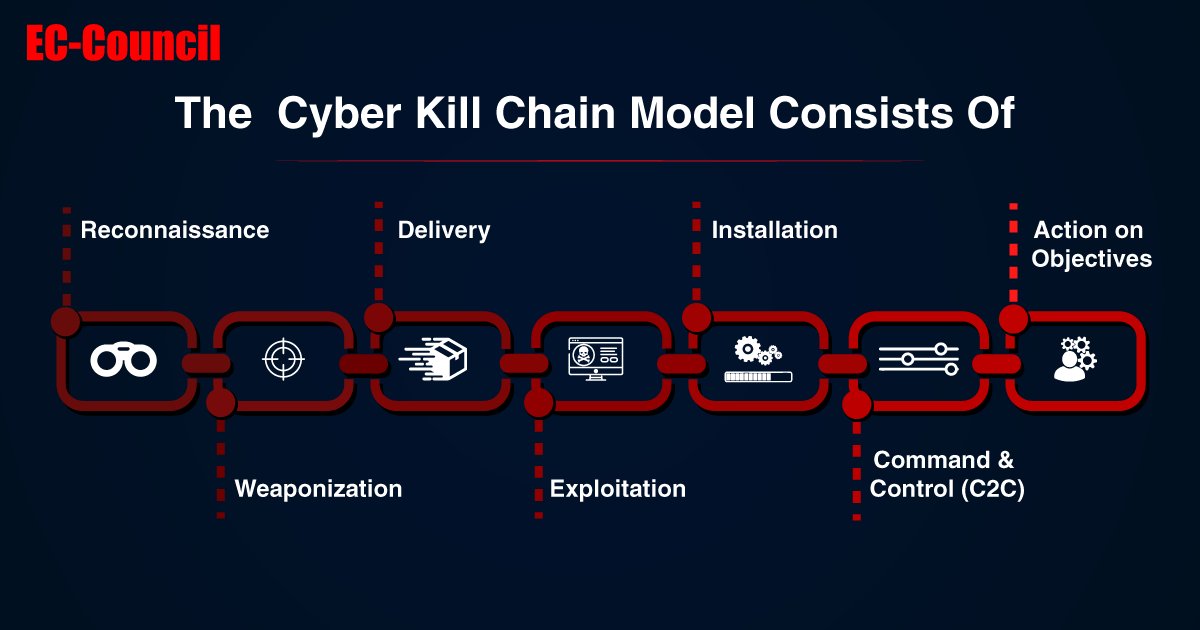
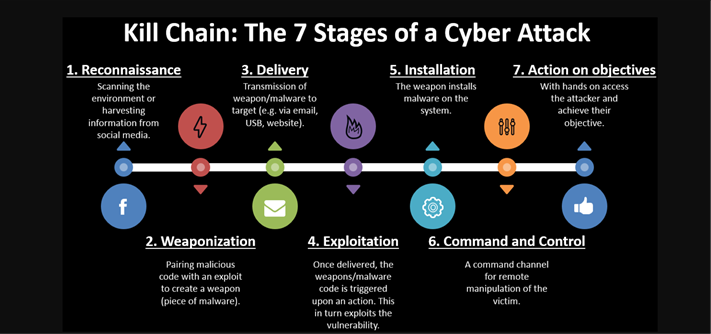
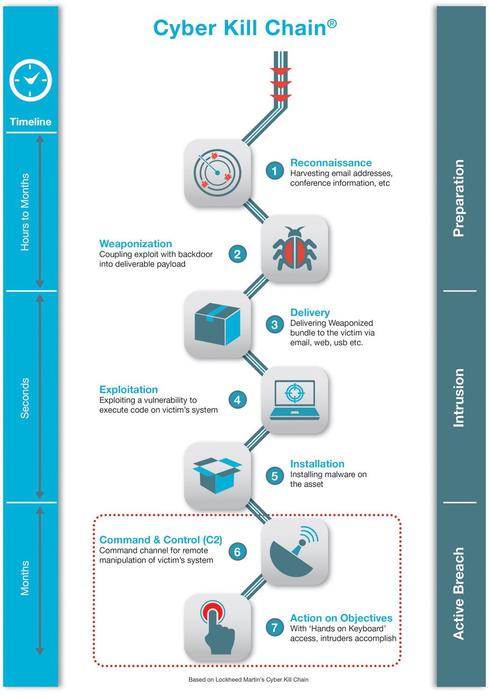
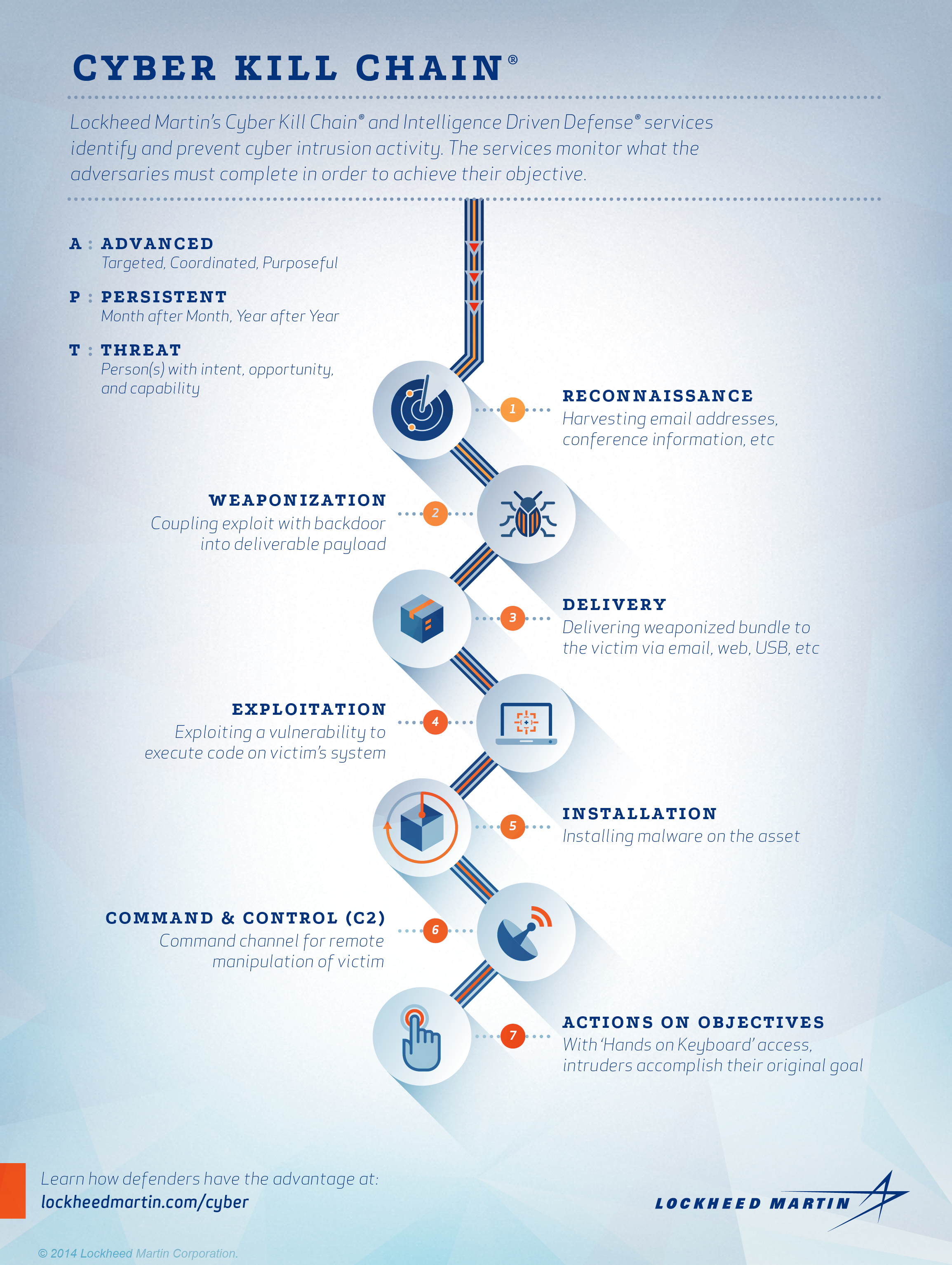
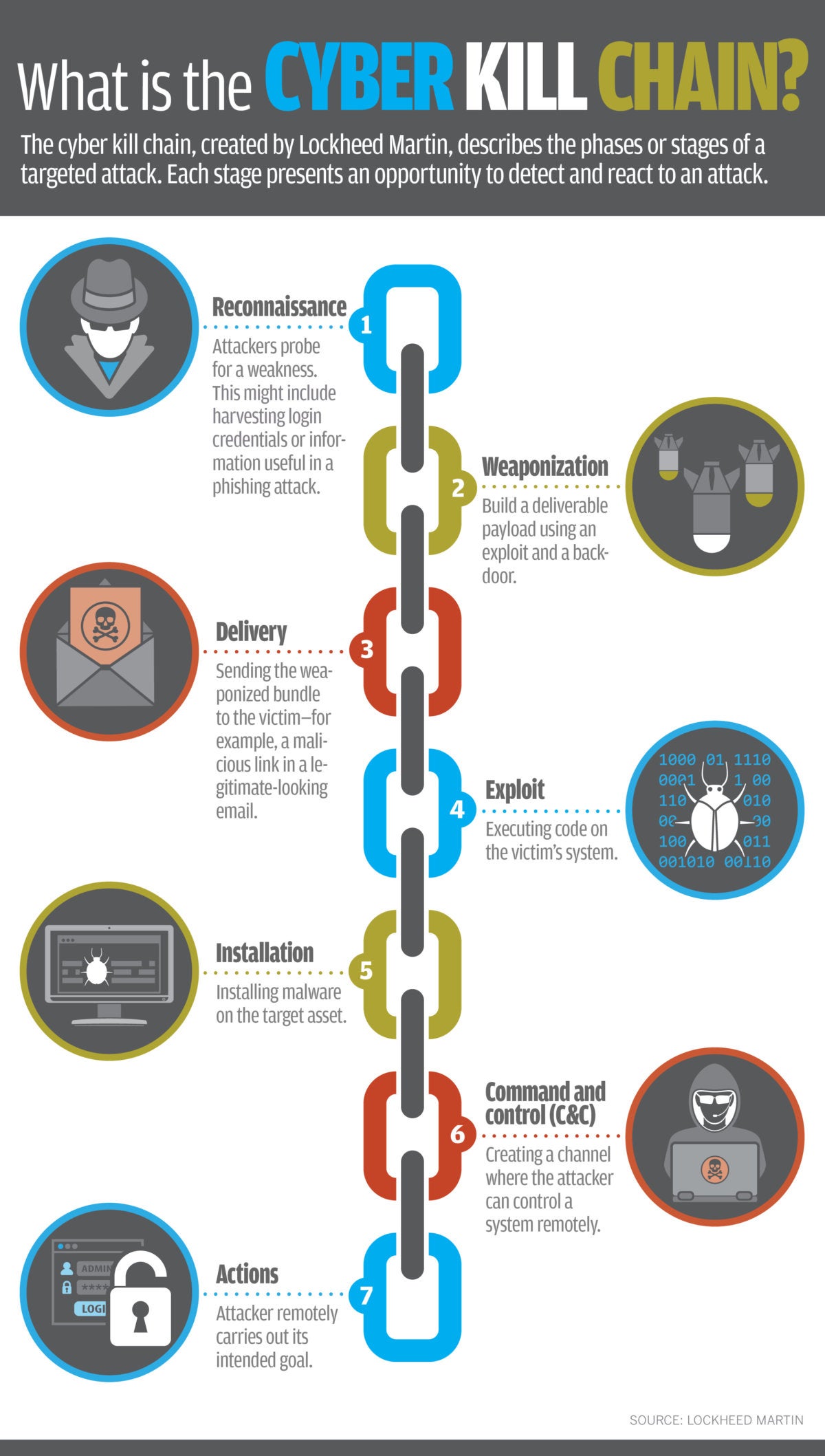
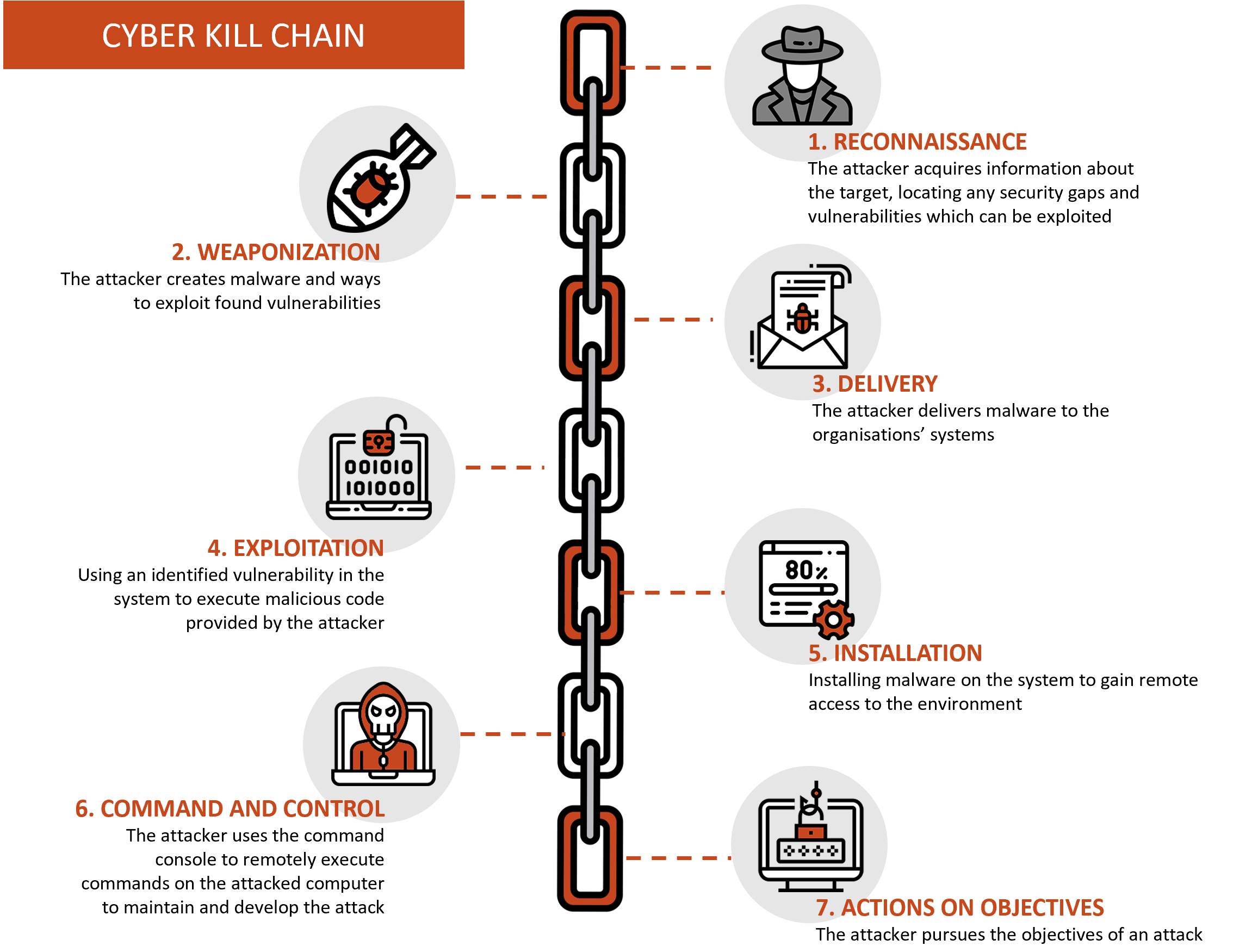
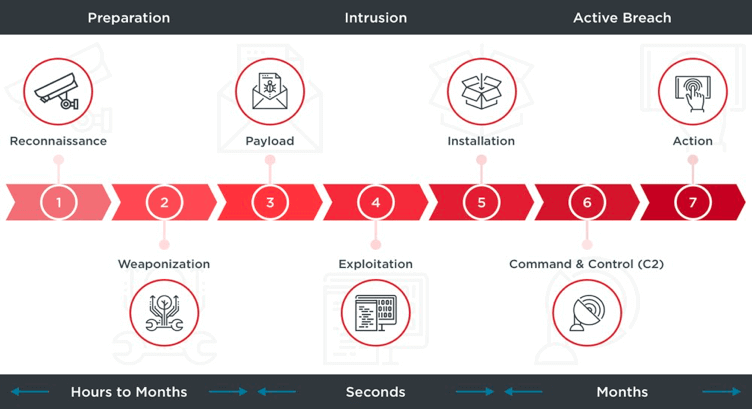
EC-COUNCIL on X: "The cyber kill chain model is made up of seven steps that hackers deploy in an attack. Take an in-depth look into these steps: https://t.co/lEwJMbIa7h #eccouncil #cybersecurity #CTIA #ThreatIntelligence #

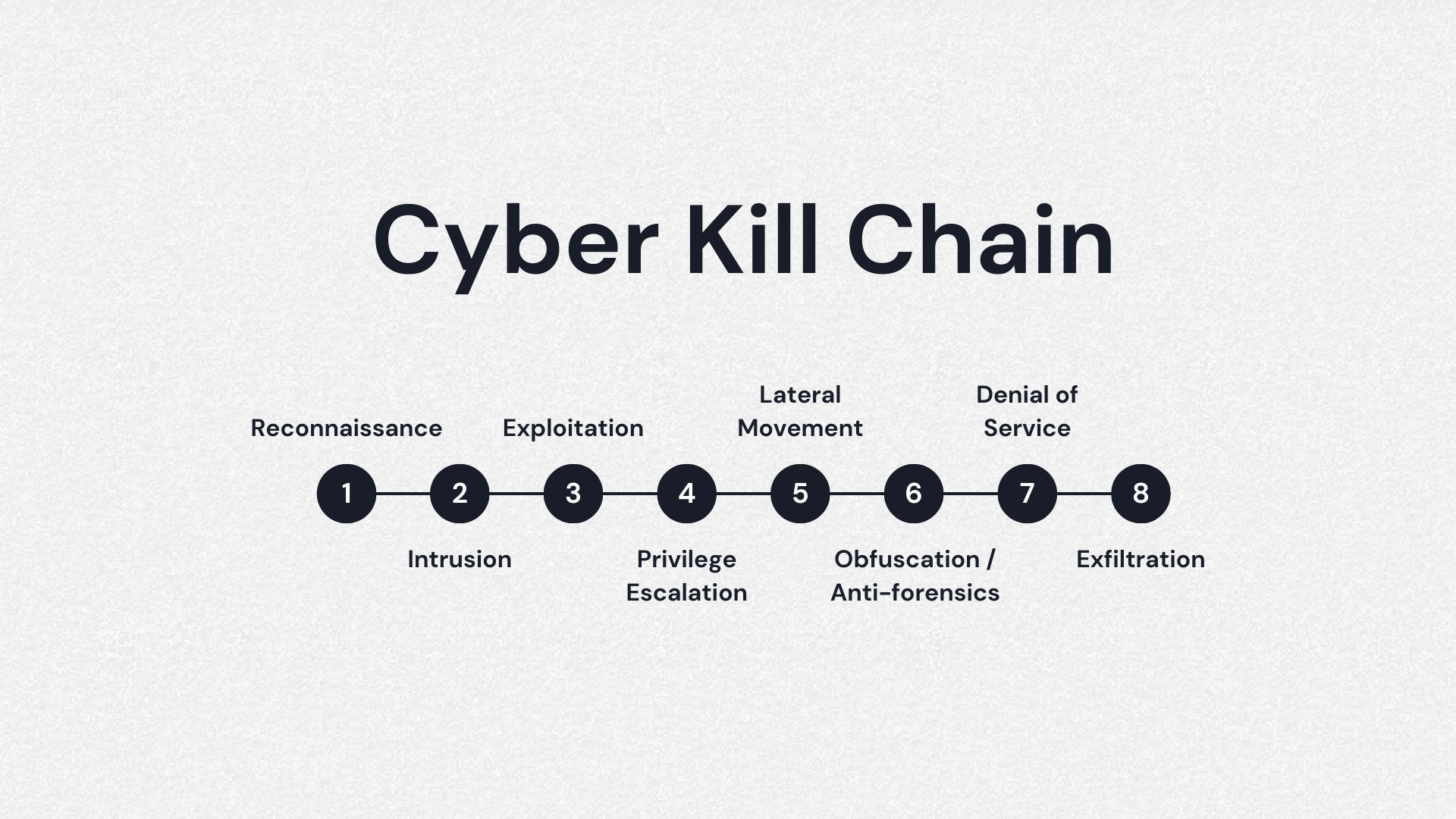
DOD's Utilization of a Cyber Kill Chain Framework to Quantify Cyber Security Investments: Part 3 of the Key Cyber Defense Strategies Series - Government Technology Insider
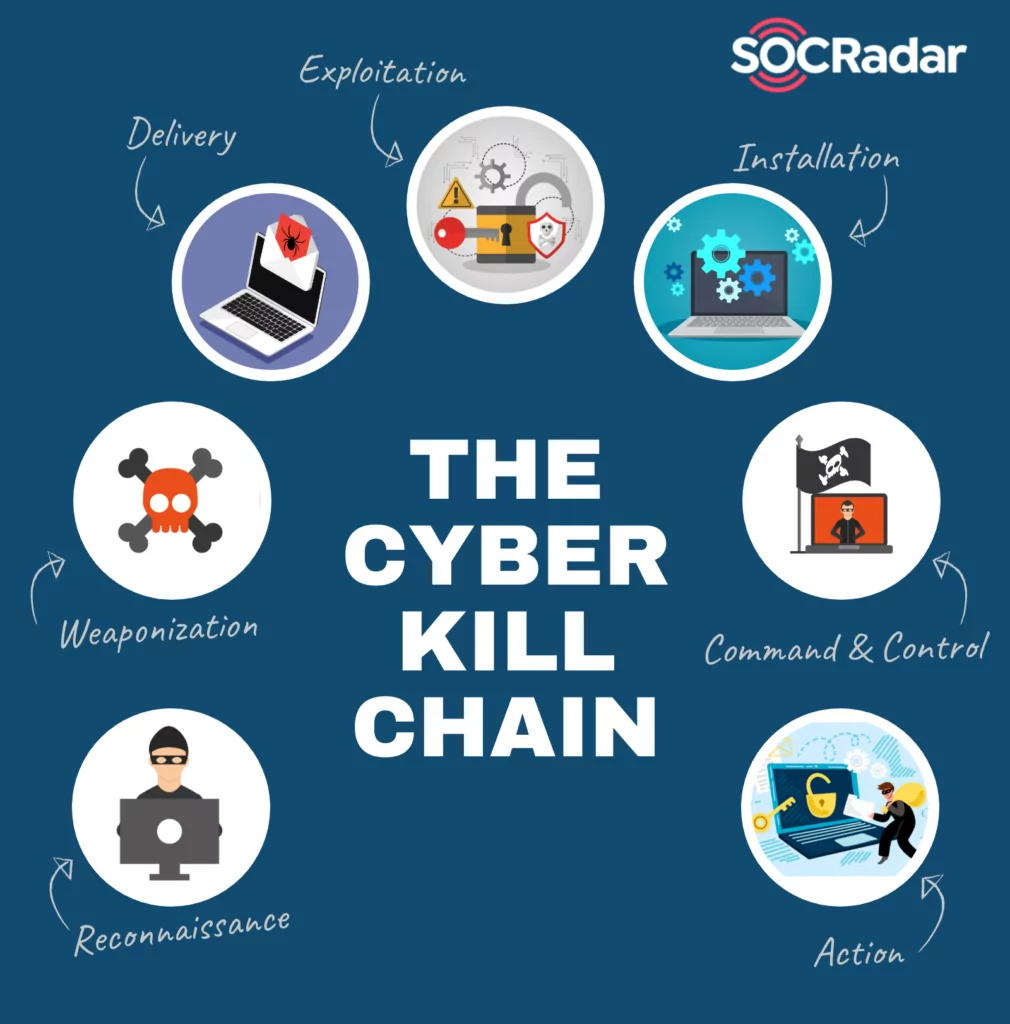
Applied Explanation of the “Cyber Kill Chain” Model as a Cyber Attack Methodology | by Ibrahim Akdağ| Ph.D. | Medium

EC-Council - The cyber kill chain helps prepare the organization for all common threats such as network breaches, data thefts, ransomware attacks, and advanced persistent attacks. Let's read more about the cyber
Is the Cyber Kill Chain Model the Ultimate Solution to Rising Ransomware Attacks? - United States Cybersecurity Magazine
![Lockheed Martin Cyber Kill Chain (CKC) [22] seven steps. The part that... | Download Scientific Diagram Lockheed Martin Cyber Kill Chain (CKC) [22] seven steps. The part that... | Download Scientific Diagram](https://www.researchgate.net/publication/335024682/figure/fig1/AS:789313017098241@1565198296990/Lockheed-Martin-Cyber-Kill-Chain-CKC-22-seven-steps-The-part-that-is-specified-with.png)




![PDF] The Industrial Control System Cyber Kill Chain | Semantic Scholar PDF] The Industrial Control System Cyber Kill Chain | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/db9041bc1cb494fafec5b04783f3d9623393331a/21-Figure7-1.png)