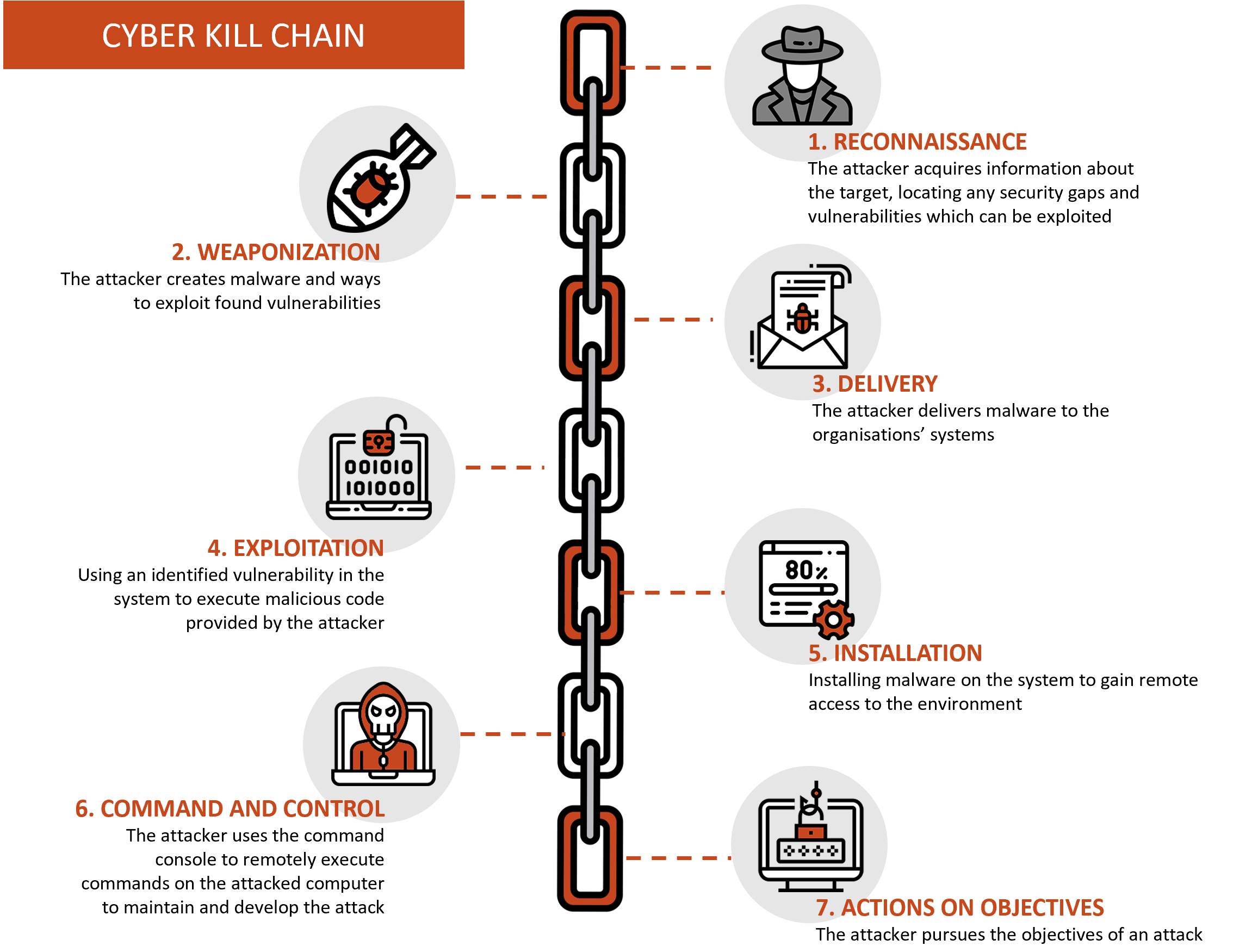
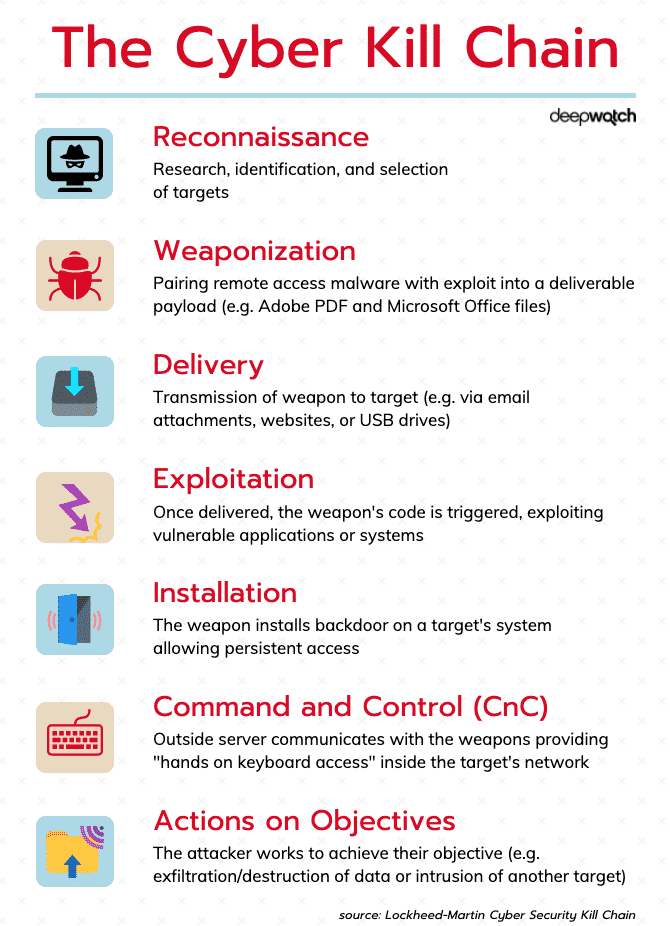
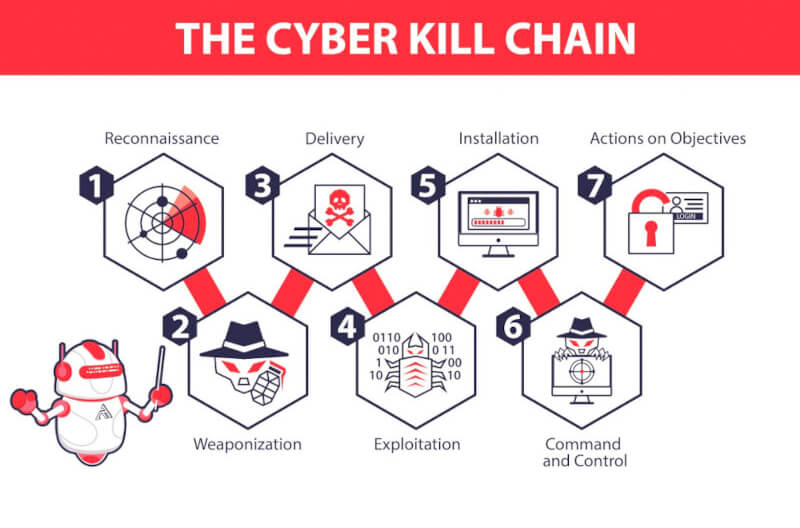
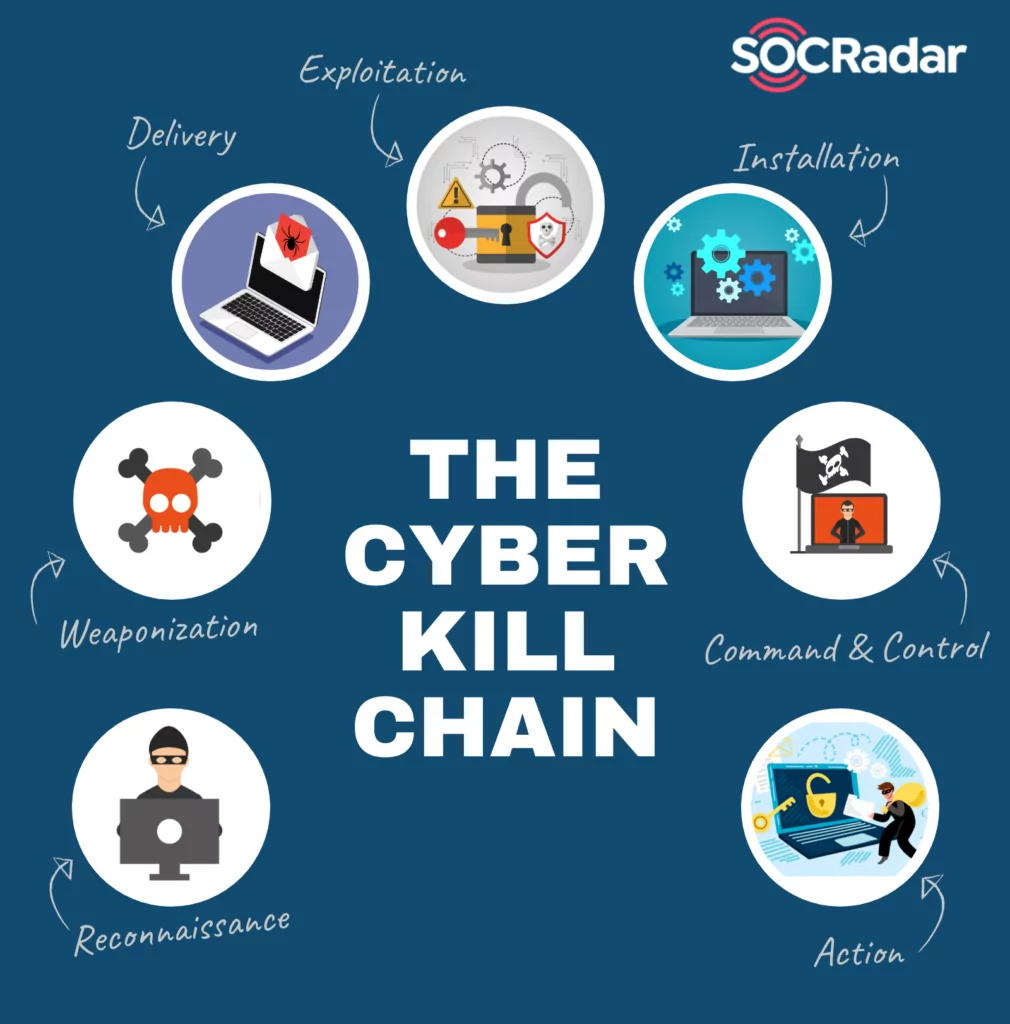
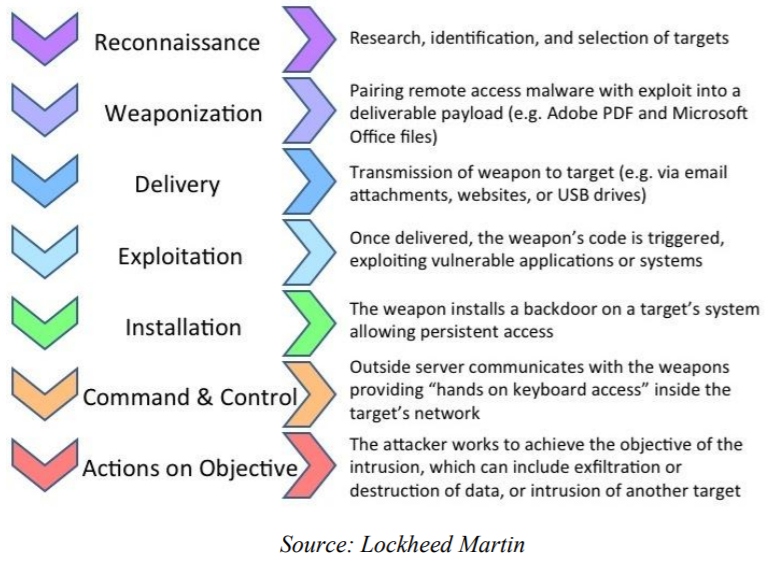
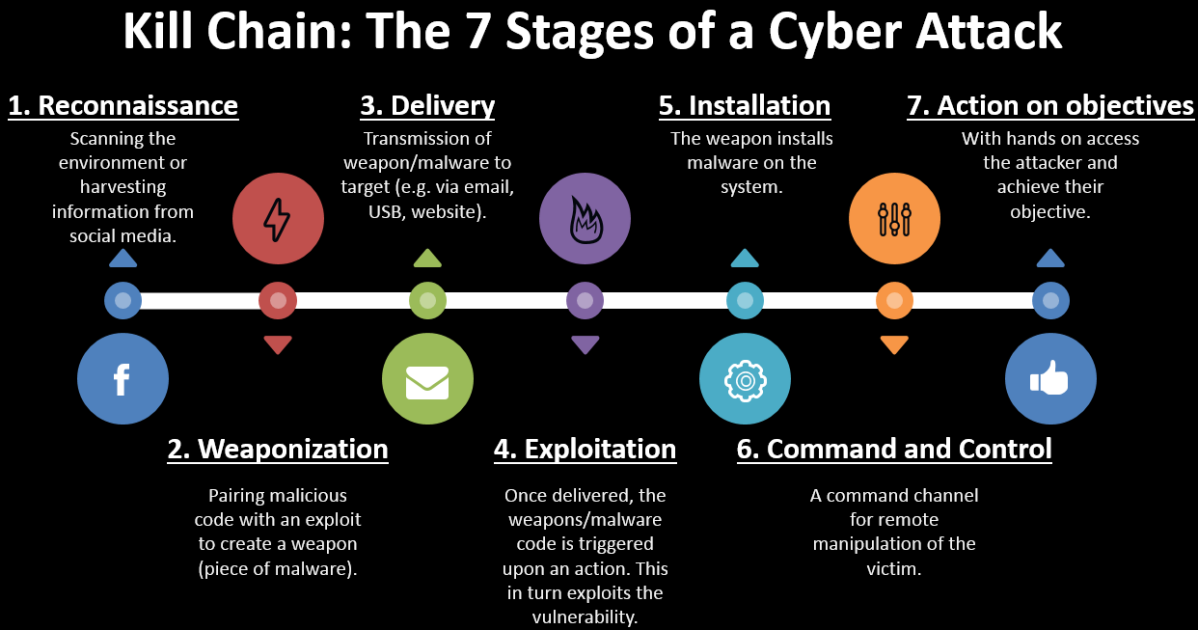
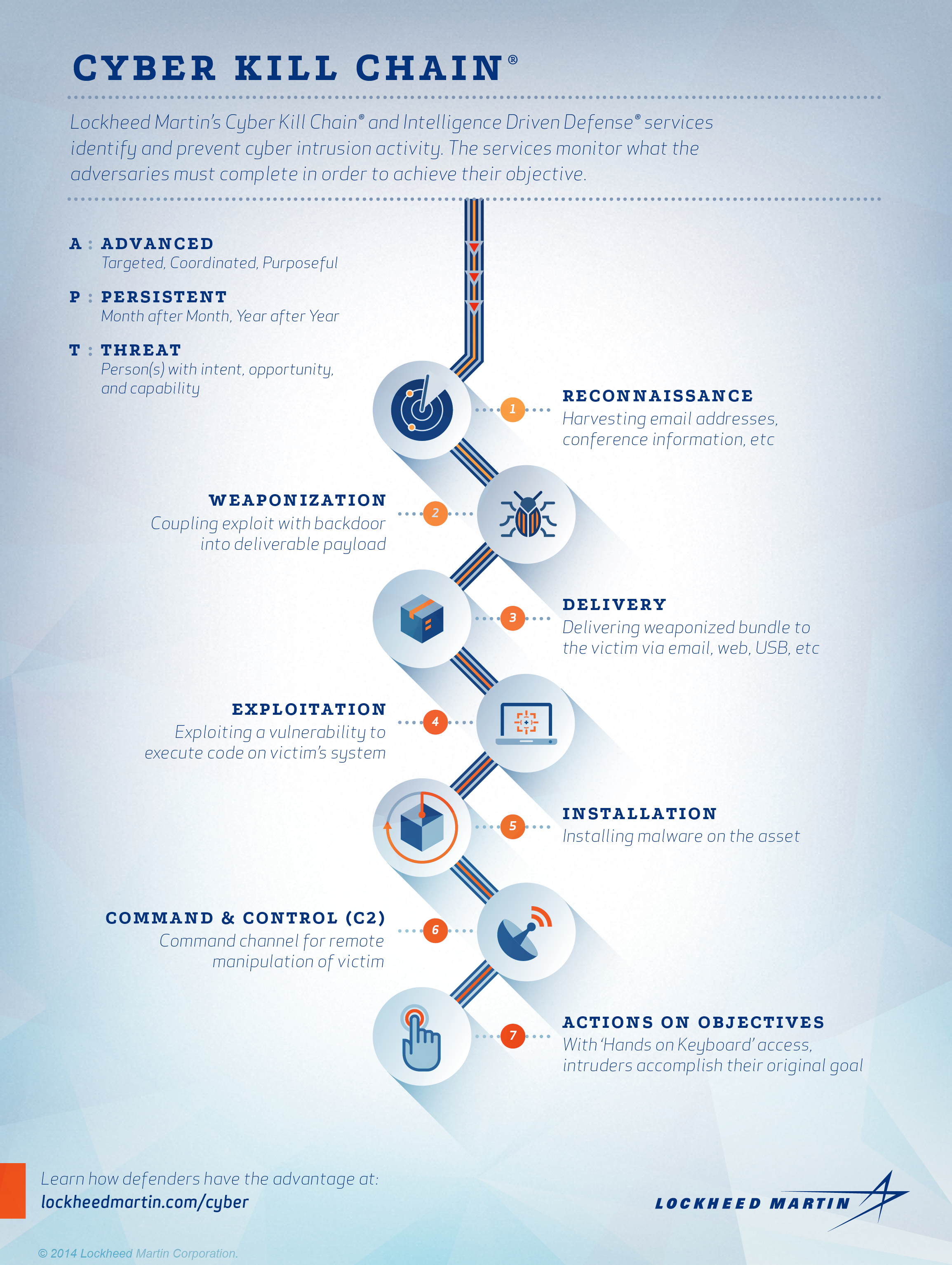
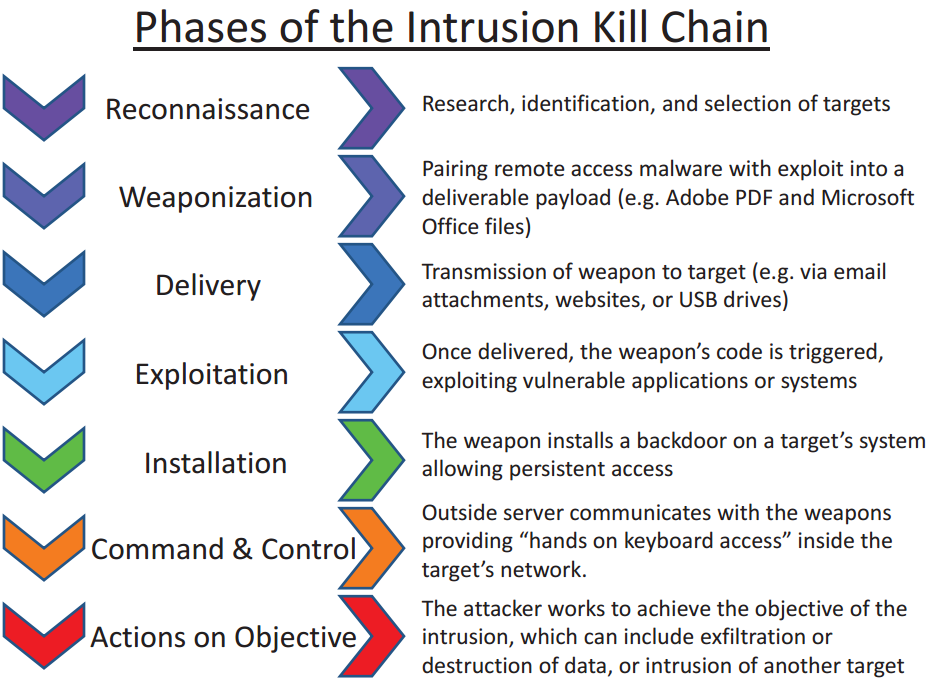
EC-Council - The cyber kill chain helps prepare the organization for all common threats such as network breaches, data thefts, ransomware attacks, and advanced persistent attacks. Let's read more about the cyber
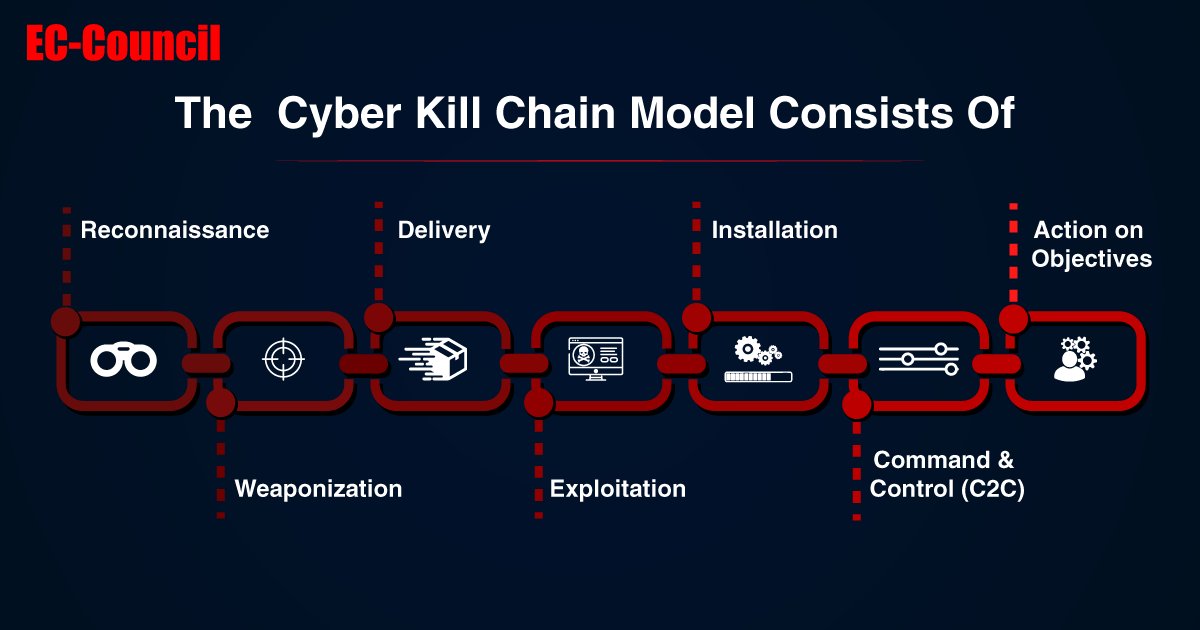
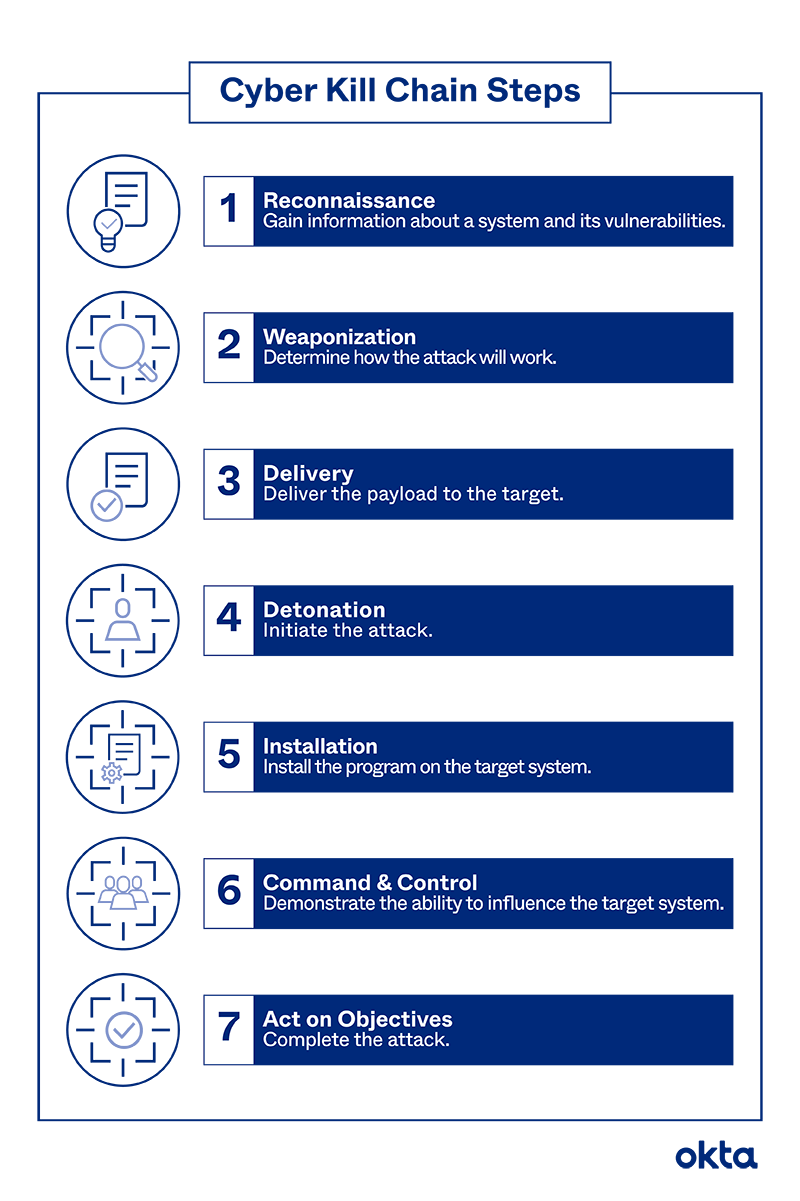
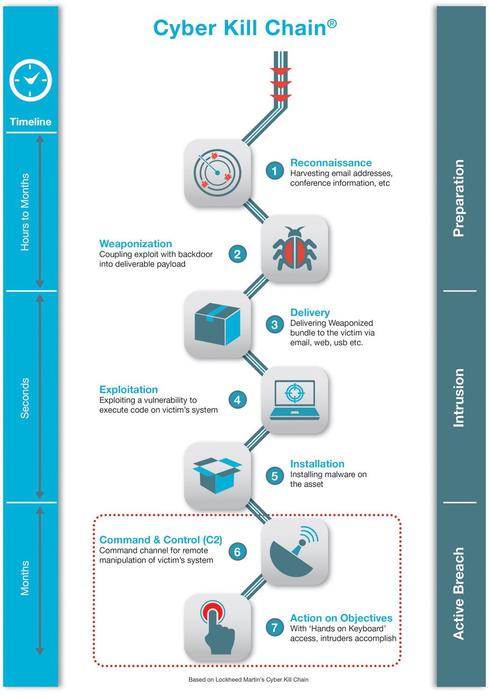
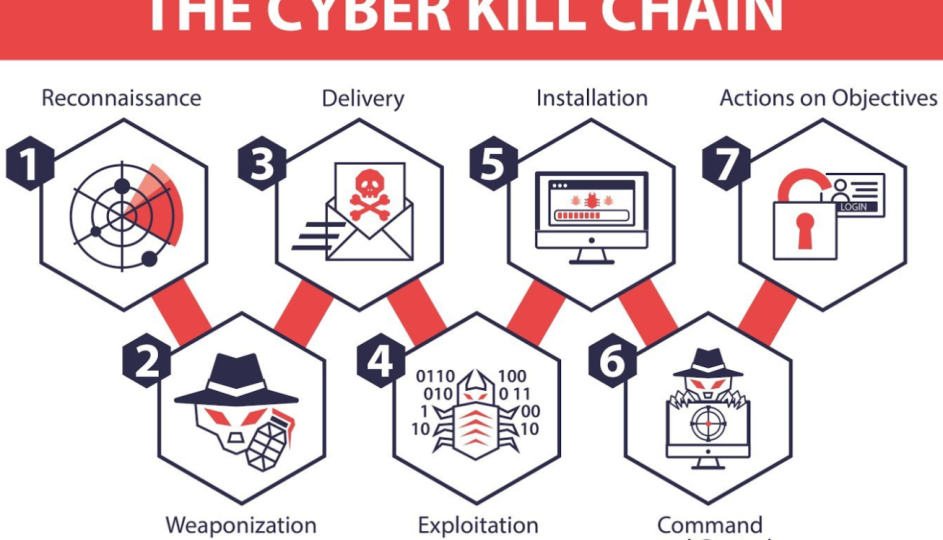
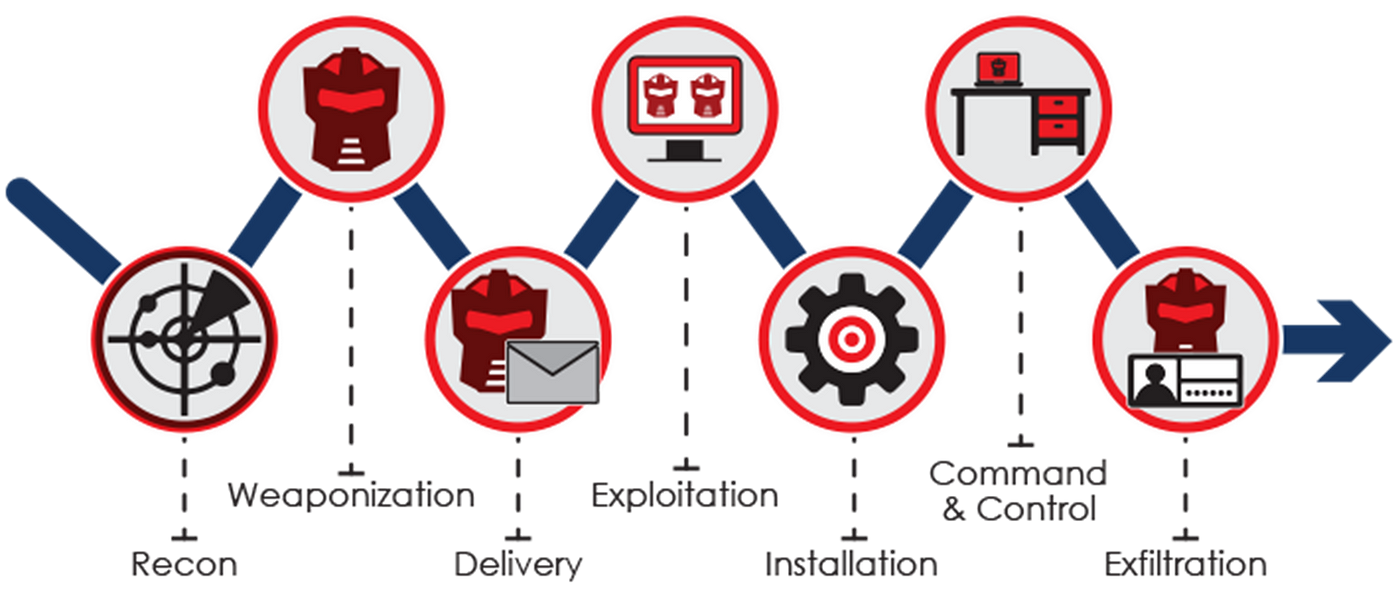
EC-COUNCIL on X: "The cyber kill chain model is made up of seven steps that hackers deploy in an attack. Take an in-depth look into these steps: https://t.co/lEwJMbIa7h #eccouncil #cybersecurity #CTIA #ThreatIntelligence #